- Home
- Education Sector
- Azure Lab Services Blog
- Use labs without registering/joining to AD/AAD
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
To make labs easy to set up and manage, Azure Lab Services is designed with no requirement to register/join lab VMs to either Active Directory (AD) or Azure Active Directory (AAD, or now also called Entra Id). As a result, Azure Lab Services doesn’t currently offer built-in support to register/join lab VMs. There are some key advantages with this approach:
- Quick and easy setup – To give students access to a lab and VM, your IT department doesn’t need to set up AD/AAD. Instead, students log in to lab VMs using a local account on the VM and can use a variety of account types to sign-in to a lab. Because of the reduced infrastructure involved, setting up and using Azure Lab Services in your environment is quick and easy. Teachers can independently set up, manage, and delete labs without help from your IT department.
- Lower management overhead – There is overhead with managing joined/registered devices in AD/AAD, which goes away with Azure Lab Services since registering/joining lab VMs is a non-requirement. This means no extra work is involved for your IT department to clean up and manage devices in AD/AAD.
- Ensure network isolation – Labs are completely isolated from your network which is ideal when you want to give students admin permission on their lab VMs, especially for networking, cybersecurity, and system admin classes.
We recognize that you may have scenarios where you want to register/join lab VMs. For example, you may want to increase VM security by using tools such as Intune or group policies to control user activity. Support for AAD joining lab VMs is being considered for the upcoming product roadmap. In the meantime, we recommend that you don’t attempt to register/join lab VMs to either AD or AAD.
In the rest of the blog post, we explain the limitations with the current experience and why we don’t recommend that you register/join lab VMs. In a future blog post, we’ll also talk about other ways that you can increase VM security without having to register/join lab VMs.
Thanks,
Azure Lab Services team
-------------------------------------------------------------------------------------------------------------------
Why we don’t recommend registering/joining lab VMs
To provide clarity, let’s first define common AD/AAD configurations and the options with each one to register/join computers.
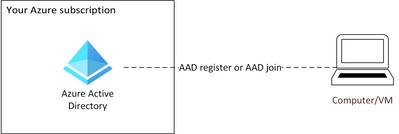
Full-cloud AAD configuration
In a full-cloud AAD configuration, your organization uses AAD and AAD Domain Services to manage computers/users. AAD is a cloud-based, Microsoft managed directory service that typically only requires that a computer has access to the internet. This enables users to either AAD register or AAD join their computers directly to your AAD in the cloud.
Figure 1 Full-cloud AAD configuration
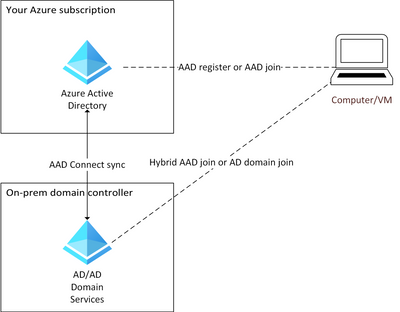
Hybrid AD/AAD configuration
In a Hybrid AD/AAD configuration, a computer joins AD Domain Services and AAD directories to enable management features of both directory services. Your on-prem AD is connected to AAD using Azure AD Connect which syncs your on-prem AD users/computers to AAD. This configuration gives several options to join/register computers:
- AAD register – Users can AAD register their computers directly to your AAD.
- AAD join – Users can AAD join their computers directly to your AAD.
- Hybrid AAD join – IT admins can domain join computers to your on-prem AD, which also automatically joins computers with AAD in the cloud. This option requires network line-of-sight from the computer to your domain controller that exists either on-prem or in Azure.
- AD domain join – It’s also possible for IT to only join computers to your on-prem AD and filter the computers from syncing to AAD. Again, network line-of-sight is required from the computer to your domain controller.
Figure 2 Hybrid AD/AAD configuration
Here’s a table that compares the capabilities that are enabled depending on the register/join option being used:
|
|
Capability |
AAD register |
AAD join |
Hybrid AAD join |
AD domain join |
|
1. |
Students can sign-in to their computer with their AD/AAD credentials |
No |
Yes |
Yes |
Yes |
|
2. |
Students have single sign-on (SSO) access to cloud resources |
Yes |
Yes |
Yes |
No |
|
3. |
Students have single sign-on (SSO) access to on-prem resources |
No |
Yes* |
Yes |
Yes |
|
4. |
IT admin can apply group policies |
No |
Yes |
Yes |
Yes |
|
5. |
IT admin can enroll lab VMs with Intune |
Yes |
Yes |
Yes |
No |
* Only applies to a Hybrid AD/AAD configuration
Known limitations
Next, let’s look at the limitations that currently exist with each of the register/join options. The following table provides a high-level comparison of the limitations across the different register/join types. For more detailed info, read the bullets further below.
|
|
Limitation |
AAD register |
AAD join |
Hybrid AAD join |
AD domain join |
|
1. |
Cleanup: AAD/AD device entries are orphaned at high rate |
X |
X |
X |
X |
|
2. |
Management: Management challenges due to non-unique VM names |
X |
X |
X |
X |
|
3. |
Join/register: Join/register process is complex for both students and IT |
X |
X |
X |
X |
|
4. |
Physical device requirements: The student’s physical device must also be AAD joined/registered and run Windows 10/11 |
|
X |
|
|
|
5. |
RDP connection: Students must change their RDP file to use AD/AAD account credentials |
|
X |
X |
X |
1. Cleanup: VMs are orphaned at a high-rate
When lab VMs are registered/joined, device entries in AD/AAD tend to become orphaned (or stale) at a high rate due to the transient nature of labs and their VMs. Here are common scenarios where lab VMs become orphaned:
- Republishing a lab so that all the student VMs are reimaged with the original image from the template VM. Each time that you republish, the student VMs are no longer registered/joined.
- Resetting individual VMs so that they are reimaged with the original image from the template VM. Each time a student chooses to reset their lab VM, their VM is no longer registered/joined.
- Deleting a lab or VM.
- Decreasing VM pool capacity (which may happen automatically if using Teams, Canvas, or AAD groups).
Orphaned device entries can grow at a high rate which adds management overhead for your IT department. For more information on the cleanup that is required, see the article How to: Manage stale devices in Azure AD.
IMPORTANT: A lab’s template VM shouldn’t be registered/joined to AD/AAD because this image is used to create the student VMs and can be exported to the Compute Gallery to create other labs.
2. Management: VMs have non-unique names
By default, Azure Labs doesn’t uniquely name lab VMs. For example, if you enable the Create a template virtual machine option when you create the lab, the VMs will all be named like “lab000001”. Or, if you leave this option disabled so that no template VM is created, the VMs will be named uniquely within a lab, but not across labs. With non-unique names, it’s challenging to manage lab VMs in AD or AAD, especially at scale.
If you’re an IT department or teacher that is proficient with scripting, you might consider using PowerShell to give lab VMs a unique name. However, we don’t recommend this because of the complexity involved:
- Initial renaming – Each VM must be given a unique, meaningful computer name before it can be registered/joined to AD/AAD. Renaming needs to occur after the lab VMs are published or when a lab’s VM pool size is increased.
- Subsequent renaming – Each time a lab VM is reset or republished, the VM must be given a new unique computer name. A VM shouldn’t be renamed to the same computer name that it was previously registered/joined with because this can cause conflicts in AD/AAD.
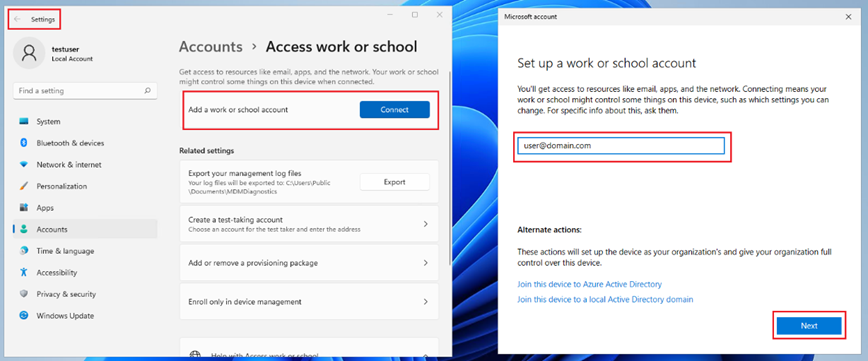
3. Join/register: Process is complex for students and IT
To AAD register or AAD join lab VMs, currently the best option is for students to self-register or self-join their lab VM using either Windows Settings or Edge. This involves several steps for students that may be too complicated and requires that their lab VM first be uniquely renamed (see bullet #2 above):
- AAD register – It’s possible for a student to sign-in to their VM using either a standard or admin local account and use the Windows Settings option to Set up a work or school account.
Figure 3 AAD register using Windows Settings
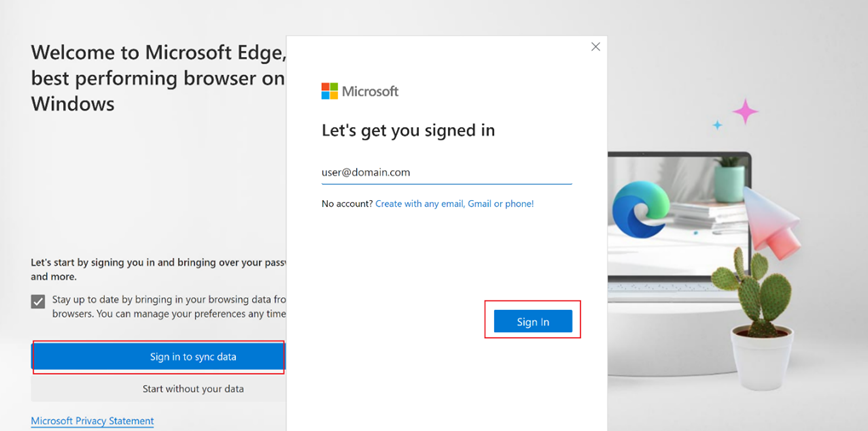
Or they can use Edge to sign-in which will AAD register their VM.
Figure 4 AAD register using Edge
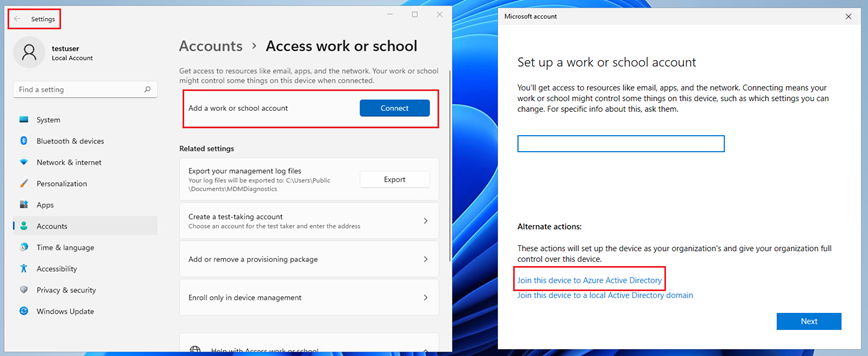
- AAD join – A student can also sign-in to their VM using the local admin account and use the Alternate actions to Join this device to Azure Active Directory in Windows Settings.
Figure 5 AAD join using Windows Settings
IMPORTANT: AAD join is further complicated by physical device requirements that need to be met to successfully RDP to an AAD joined VM. See the next bullet #4 for more info.
To Hybrid AAD join or AD domain join lab VMs, your IT department typically must do this because it requires admin credentials to join the VMs to AD and direct access to AD to ensure devices are properly joined. It’s possible to Hybrid AAD join and AD domain join VMs using PowerShell; however, this is complicated by the following:
- Each student VM needs to first be uniquely renamed (see bullet #2 above).
- The admin credentials that have access to join the VMs to AD need to be saved in a secure store because the script would need to reside on the lab VMs that students have access to.
- To run the scripts on student VMs to join them, your IT department would either need to use Remote PowerShell commands or Windows Task Scheduler.
Things get more complicated for AAD register, AAD join, Hybrid AAD join, or AD domain join because the steps need to be repeated in the following scenarios:
- Republishing a lab so that all the student VMs are reimaged with the original image from the template VM. Each time that you republish, the student VMs are no longer registered/joined and you need to repeat the process to give them a new unique name and register/join them again.
- Resetting individual VMs so that they are reimaged with the original image from the template VM. Each time a student chooses to reset their lab VM, their VM is no longer registered/joined and you need to repeat the process to give the VM a new unique name and register/join the VM again.
- Increasing VM pool capacity (which may happen automatically if using Teams, Canvas, or AAD groups).
4. Physical device requirements: Win 10/11 and AAD joined/registered
To successfully sign-in and connect to an AAD joined lab VM, the physical device must adhere to the following requirements:
- The lab VM and the physical device the student connects from must both be running Windows 10 or newer. Windows 7/8.1 and Windows Server are not supported for AAD Join. Windows Home Editions do not support Azure AD join.
- Both the physical device the student connects from, and the lab VM must run supported versions of Windows 10/11.
- The physical device must also be AAD registered, AAD joined, or Hybrid AAD joined.
- Both the physical device and lab VM must be in the same AAD tenant.
This means that students can’t use a Chromebook, Mac, or Linux device to connect to an AAD joined lab VM.
IMPORTANT: These physical device requirements only apply to VMs that are AAD joined. They do not apply to VMs that are AAD registered, Hybrid AAD joined, or AD domain joined.
5. RDP connection: File defaults to local account
One reason that IT departments and teachers want to join lab VMs, is to enable an SSO experience so that students can sign-in to their lab VM with their AD/AAD credentials and access on-prem and/or Microsoft 365 (M365) cloud resources such as OneDrive. However, students must know how to change the RDP connection file’s default account to sign-in with their AD/AAD credentials to a VM that is AAD joined, Hybrid AAD joined, or AD domain joined. These steps may add too much complexity and be error-prone for students.
After the student downloads the RDP connection file and opens the RDP client, they need to change from the default local account to their AD/ADD account (e.g., user@domain.com or AzureAD/user@domain.com). To avoid repeating this step each time the student logs in, they can also edit the RDP file to use their domain account by default and save the RDP file to their physical device.
IMPORTANT: These steps to change the default account in the RDP file are only needed when a lab VM is AAD joined, Hybrid AAD joined, or AD domain joined. AAD register does not support signing into the lab VM using their AD/AAD credentials.
Figure 6 Prompt to change default RDP account
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.